Active Directory Audit

Ransomware attacks are on the rise, and the ones with the highest impact take over the whole Active Directory. We must secure these systems to minimize the risk of having our data encrypted and put up for sale on the internet!

Ransomware attacks are on the rise, and the ones with the highest impact take over the whole Active Directory. We must secure these systems to minimize the risk of having our data encrypted and put up for sale on the internet!
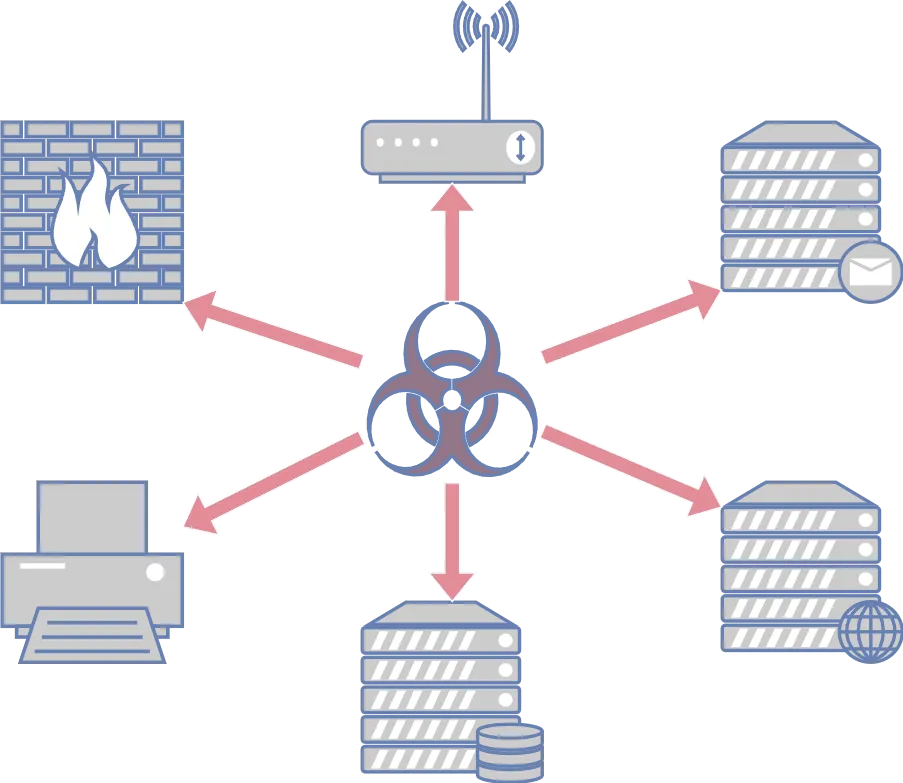
What if one of your employees clicks on the wrong email attachment? Will you be able to stop the attack, or will the attackers be able to move laterally from there and take over all your systems? This is why you should conduct an internal infrastructure penetration test. The internal system is just one wrong click away from being “public”.
Cloud services offer many new opportunities for companies. However, they also present many dangers that can be exploited by attackers. Therefore, it is essential that these services are configured correctly. This configuration is checked in a Cloud Infrastructure Audit.
Realistic attack scenarios and typical attack paths are recreated. The goal is security validation: How well is your organization prepared for real-world attacks? How do your teams respond? The focus is on threat detection and security posture.

EntraID (Microsoft Entra ID) is Microsoft’s central identity and access management (IAM) solution—especially in Microsoft 365 environments—and forms the basis for single sign-on (SSO) and access control. A misconfiguration can lead to unauthorized access to company resources or facilitate social engineering attacks. Therefore, this component must be thoroughly tested.
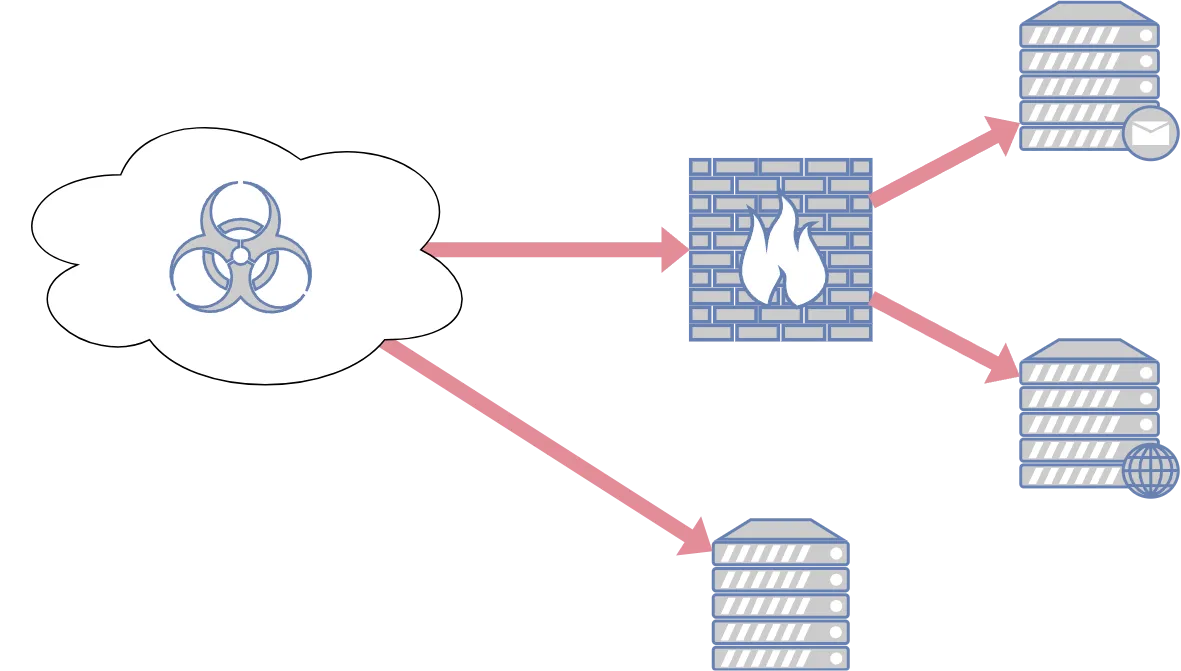
If your system is exposed to the internet, it could potentially be hacked by anyone. Okay, I exaggerate a bit, but I think you understand. Vulnerabilities in your external infrastructure can lead to very bad press and threaten your customers’ personal information. So, it’s better to check once more.
For companies that haven’t yet thoroughly explored cybersecurity, VidraSec offers a Starter Pack. The goal is to provide these companies with an initial overview of their security posture. The results from this project serve as the foundation for prioritizing the remediation of vulnerabilities and implementing processes to strengthen information security.
Most cyber attacks begin with a human error. Someone has set a weak password or opened the wrong email attachment. Therefore, it is essential that all employees are trained on how to behave correctly.
Vulnerabilities in web applications can be very problematic. In the worst case, the entire web server is taken over or confidential customer data is stolen. Therefore, it is especially important to thoroughly test these applications.