Active Directory Audit

Ransomware attacks are on the rise, and the ones with the highest impact take over the whole Active Directory. We must secure these systems to minimize the risk of having our data encrypted and put up for sale on the internet!

Ransomware attacks are on the rise, and the ones with the highest impact take over the whole Active Directory. We must secure these systems to minimize the risk of having our data encrypted and put up for sale on the internet!
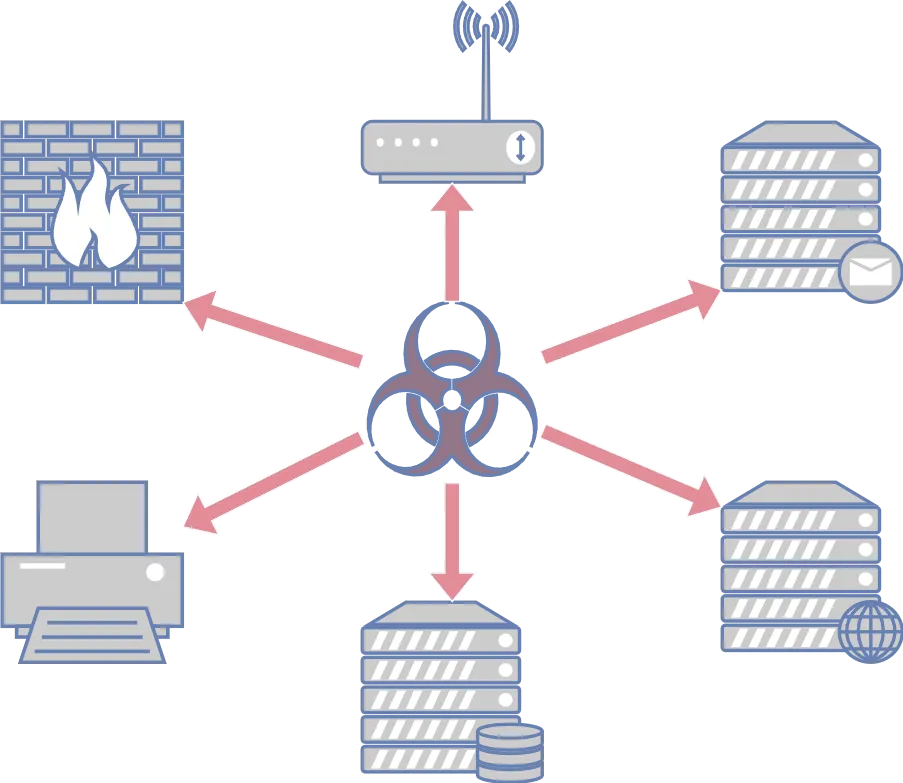
What if one of your employees clicks on the wrong email attachment? Will you be able to stop the attack, or will the attackers be able to move laterally from there and take over all your systems? This is why you should conduct an internal infrastructure penetration test. The internal system is just one wrong click away from being “public”.

Kerberos works similarly to a passport: A passport authority issues the passport after the person has identified themselves. With this passport, they can then go to the border and prove their identity.
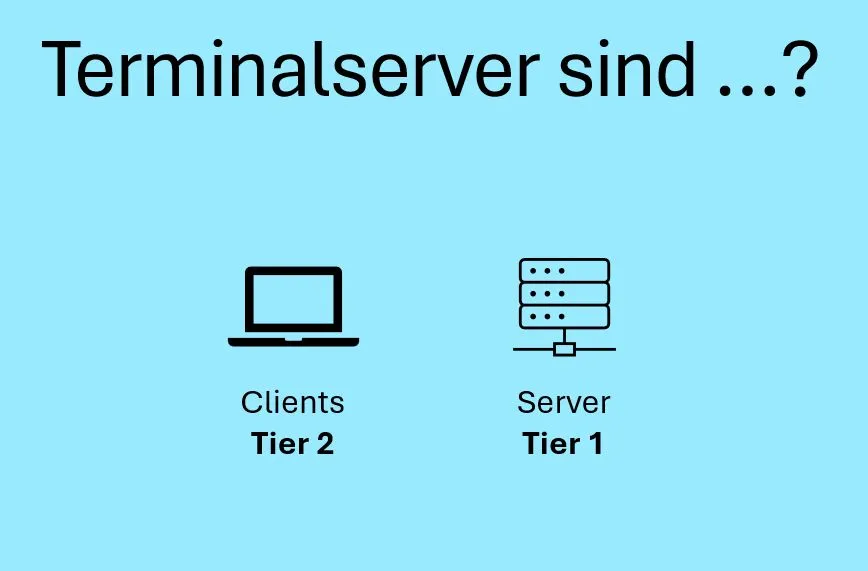
In this blog post, I will briefly address two often overlooked vulnerabilities and misconfigurations in the Active Directory Tiering model. Specifically, I will focus on the mishandling of terminal servers and the helpdesk user group.
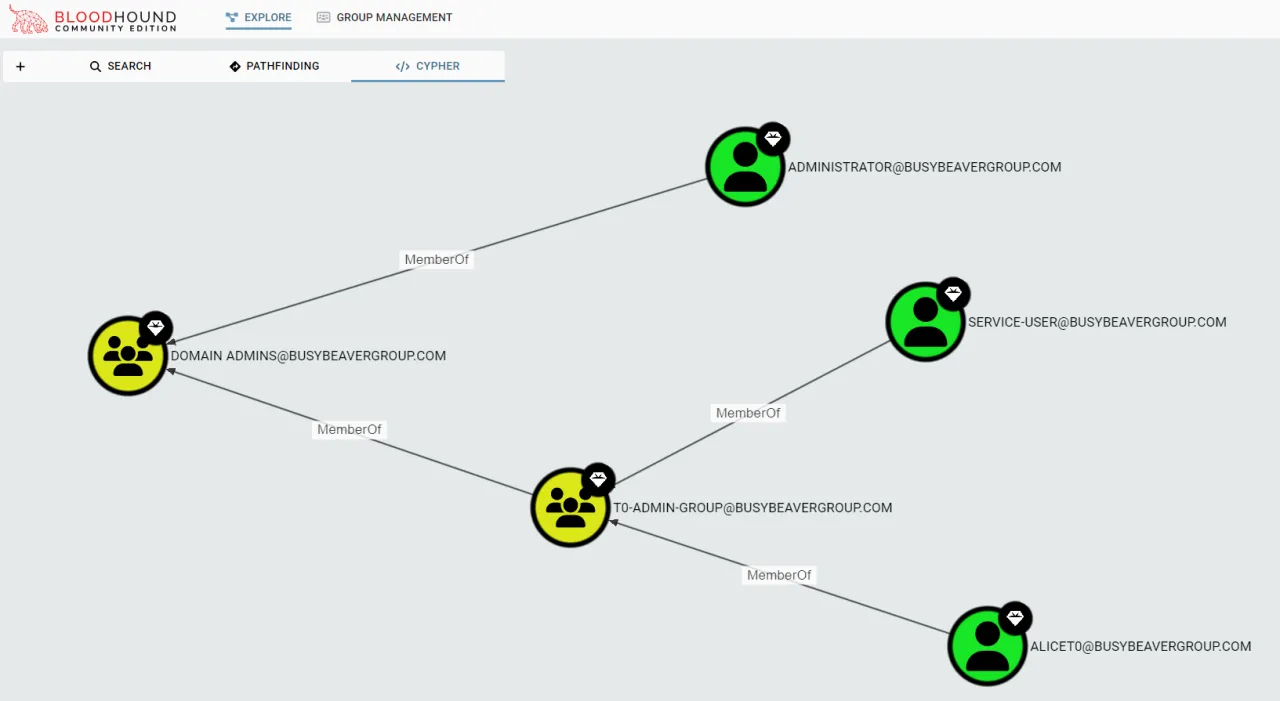
BloodHound is a tool developed by penetration testers and red teamers to better identify and visualize attack paths in Active Directory. However, that doesn’t mean it can’t also be used effectively by admins or the blue team.
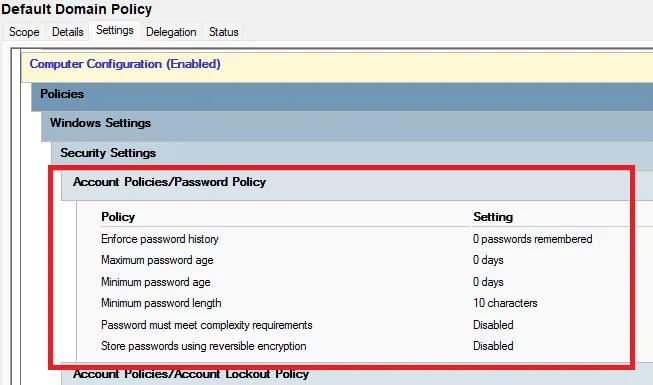
Unfortunately, setting a good password policy for Active Directory is difficult. This is also because there are several best practices that sometimes contradict each other. In this post, I will try to address the various best practices and give my own recommendation.

This is the first part of a series in which we look into default insecure configurations in Active Directory. This part covers the Pre-Windows 2000 Compatible Access group. What is it? What are the risks? And what can we do about it?